Using automation to enhance cybersecurity risk management
News & Insights
5 Min Read
The Power of Automation: Enhancing Cybersecurity Risk Management In today's fast-paced digital landscape, cybersecurity risks are constantly evolving. Manually managing these risks is not only time-consuming but also often insufficient. The solution? Automation. By leveraging automation technologies, organizations can significantly enhance their cybersecurity risk management processes, becoming more efficient, proactive, and resilient against emerging threats.
This post will explore how automation can transform cybersecurity risk management, providing actionable insights into practical applications and demonstrating how these tools are changing the game.
Why Automation is Critical for Cybersecurity Risk Management
Before diving into the specifics, let’s understand why automation is so critical:
Speed and Efficiency: Automation enables faster and more efficient responses to threats, reducing the time required for manual tasks.
Reduced Human Error: It minimizes human error, ensuring greater accuracy in security processes.
Proactive Security: Automation enables proactive detection and prevention of threats, rather than reactive responses.
Scalability: It allows security teams to handle large volumes of data and increasing workloads without being overwhelmed.
Improved Compliance: Automation can streamline compliance efforts, ensuring that security policies are consistently enforced.
Cost Savings: It reduces the need for manual labor, freeing up valuable resources and reducing operational costs.
Real-Time Monitoring: Automation can provide real-time monitoring of systems, enabling quicker response to anomalies and attacks.
Key Areas Where Automation Enhances Cybersecurity Risk Management
Here are some key areas where automation can make a significant impact on cybersecurity risk management:
Vulnerability Management:
Automated Scanning: Automate vulnerability scanning to continuously identify weaknesses in your systems.
Prioritization of Vulnerabilities: Automatically prioritize vulnerabilities based on their severity and potential impact.
Automated Patch Management: Automate the deployment of security patches and updates to address vulnerabilities quickly.
Integration with Remediation Tools: Automate the process of triggering remediation actions.
Threat Detection and Response:
Security Information and Event Management (SIEM): Automate log collection, analysis, and correlation to detect suspicious activity.
Endpoint Detection and Response (EDR): Automate endpoint threat detection and response, including isolation of infected devices.
Automated Threat Intelligence: Automate the collection and analysis of threat intelligence data.
Incident Response Playbooks: Automate incident response playbooks to quickly and consistently respond to different types of security incidents.
Access Management:
User Provisioning and Deprovisioning: Automate the process of granting and revoking user access to systems and applications.
Privileged Access Management (PAM): Automate the management of privileged accounts and access permissions.
Access Reviews: Automate periodic access reviews to identify and remove unnecessary permissions.
Compliance Management:
Automated Compliance Checks: Automate compliance checks to ensure adherence to regulatory requirements.
Policy Enforcement: Automate the enforcement of security policies across your organization.
Compliance Reporting: Automate the generation of compliance reports for auditors.
Configuration Management:
Automated Configuration Scans: Automate the scanning of systems for misconfigurations and compliance issues.
Remediation of Misconfigurations: Automatically remediate misconfigurations based on defined policies.
Configuration Baselines: Automatically enforce configuration baselines across all systems.
Security Awareness Training:
Automated Training Programs: Automate the delivery of security awareness training modules to employees.
Phishing Simulations: Automate phishing simulations to test employee awareness of phishing attacks.
Progress Tracking: Track employee progress and identify areas for improvement.
Data Security and Protection:
Automated Data Classification: Automatically classify data based on its sensitivity.
Data Loss Prevention (DLP): Automate DLP policies to prevent unauthorized data leaks.
Encryption Key Management: Automate the rotation and management of encryption keys.
Implementing Automation in Your Cybersecurity Program
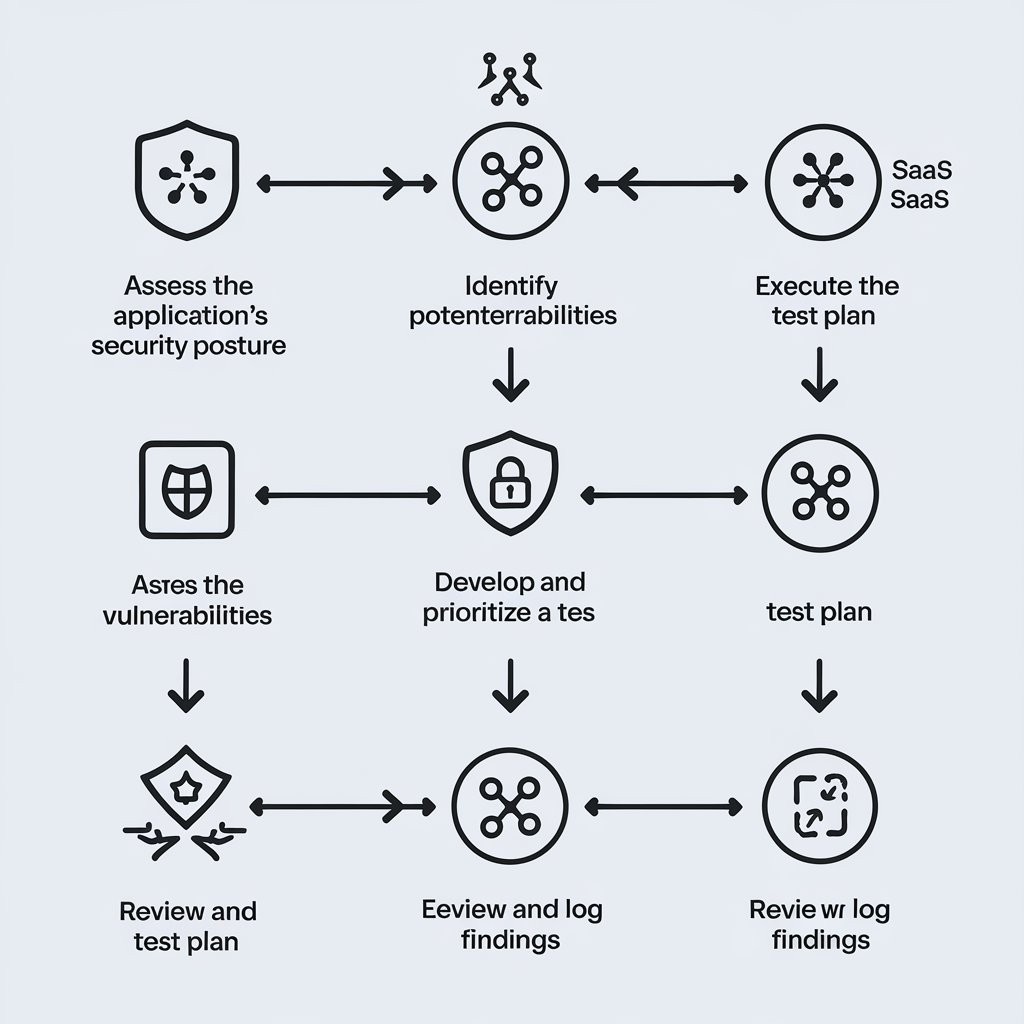
Here are key steps to successfully implement automation in your cybersecurity risk management:
Identify Manual Processes: Identify which tasks within your cybersecurity risk management processes are currently performed manually.
Define Automation Objectives: Define specific objectives for automation, focusing on areas where automation can provide the greatest benefit.
Choose the Right Tools: Select automation tools that are suitable for your specific needs and budget.
Integrate Systems: Integrate your automation tools with your existing security systems and workflows.
Start Small and Scale Gradually: Begin with smaller automation projects and gradually expand the scope of your automation initiatives.
Monitor and Evaluate: Monitor the performance of your automated processes and make adjustments as needed. audit3aa
Join our newsletter list
Sign up to get the most recent blog articles in your email every week.