Managing security in hybrid cloud environments
News & Insights
7 Min Read
Securing the Best of Both Worlds: A Guide to Hybrid Cloud Security The hybrid cloud model – combining on-premises infrastructure with public cloud services – is increasingly popular. It offers the agility and scalability of the cloud with the control and security of a private environment. However, this hybrid approach also presents unique security challenges. Managing security across these diverse environments requires a strategic and well-planned approach.
What is a Hybrid Cloud Environment?
Before diving in, let's clarify what we mean by "hybrid cloud." It's a computing environment that combines:
On-premises infrastructure: Your existing data centers, servers, and hardware.
Public cloud services: Services provided by third-party vendors like AWS, Azure, and Google Cloud.
Interconnectedness: These environments are connected to allow seamless data and application movement between them.
The Unique Security Challenges of Hybrid Clouds
Hybrid environments are complex and present some security challenges that are not typically seen in single-environment setups. Here are some key challenges:
Inconsistent Security Policies: Security policies can vary significantly between your on-premises infrastructure and your cloud providers' environments, leading to inconsistencies and gaps in your security posture.
Visibility Gaps: The distributed nature of hybrid clouds makes it difficult to maintain a comprehensive view of your assets and security posture. Tracking data, applications, and users across different environments becomes difficult.
Identity Management Complexity: Managing user identities and access rights across different environments can be a challenge. Siloed identity systems can lead to security risks.
Compliance Headaches: Different regulations might apply to your on-premises data and cloud data. Maintaining compliance across all environments can be complex and demanding.
Increased Attack Surface: Hybrid environments have a larger attack surface due to the interconnected nature of on-premises and cloud resources, and the potential for misconfigurations.
Lack of Skilled Resources: Managing security in hybrid clouds requires specialized security skills that may be lacking in some organizations.
Key Strategies for Effective Hybrid Cloud Security
Overcoming these challenges requires a multi-pronged approach. Here are key strategies to secure your hybrid cloud environment:
Implement a Unified Security Strategy:
Centralized Security Policies: Develop consistent security policies that apply across your entire hybrid environment, covering access control, data protection, and incident response.
Security Orchestration, Automation, and Response (SOAR): Automate security tasks to improve efficiency and consistency across different environments.
Strengthen Identity and Access Management (IAM):
Centralized Identity Management: Use a centralized IAM system to manage user identities and access rights across all environments.
Multi-Factor Authentication (MFA): Enforce MFA for all users accessing your systems.
Principle of Least Privilege: Grant users only the minimum level of access required for their roles.
Regular Access Reviews: Conduct regular access reviews to revoke unnecessary access permissions.
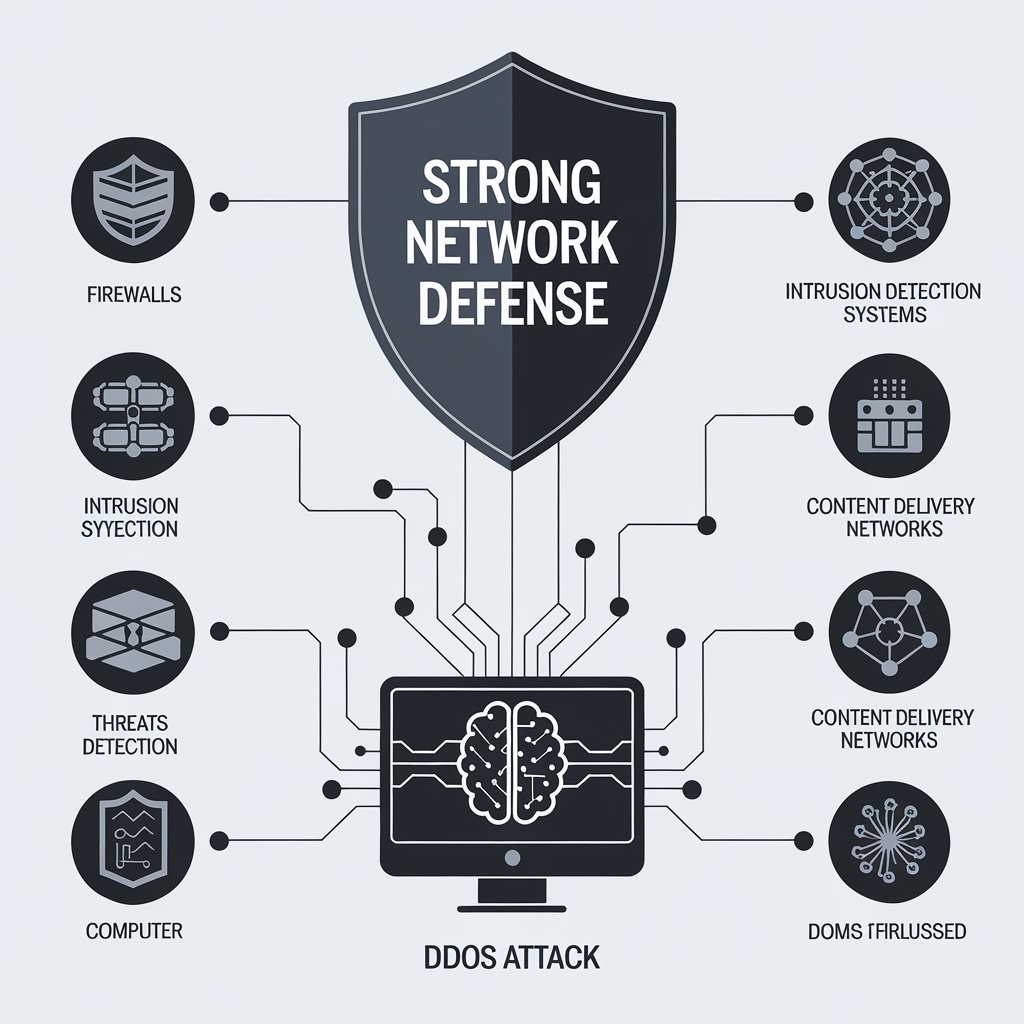
Enhance Network Security:
Microsegmentation: Divide your network into smaller segments to limit the impact of a potential breach.
Consistent Network Security Controls: Implement consistent firewall rules, intrusion detection/prevention systems (IDS/IPS), and network monitoring across all environments.
Secure VPN Connections: Use secure VPN connections to ensure encrypted communication between your on-premises infrastructure and the cloud.
Prioritize Data Protection:
Data Encryption: Encrypt data both at rest and in transit, regardless of where it’s stored.
Data Loss Prevention (DLP): Deploy DLP tools to prevent sensitive data from leaving your control.
Data Classification: Categorize data based on its sensitivity and apply appropriate security controls.
Improve Visibility and Monitoring:
Centralized Logging: Implement a centralized logging system to collect logs from all environments for unified threat detection.
Security Information and Event Management (SIEM): Use a SIEM platform to correlate security events, detect anomalies, and respond to security incidents.
Real-Time Monitoring: Monitor your cloud resources, network traffic, and user activity in real-time.
Embrace the "Shared Responsibility" Model:
Understand Responsibilities: Clearly understand the responsibilities of your cloud providers and your own security team.
Secure Cloud Configurations: Ensure you configure your cloud resources securely and according to best practices.
Cloud Security Posture Management (CSPM):
Automated Configuration Checks: Use CSPM tools to automatically assess your cloud infrastructure configurations against best practices and compliance standards.
Remediation Recommendations: Utilize CSPM to identify misconfigurations and provide remediation recommendations.
Essential Tools and Technologies:
Identity and Access Management (IAM) Platforms: Okta, Azure Active Directory, Ping Identity.
Cloud Security Posture Management (CSPM) Tools: CloudHealth, Dome9, Prisma Cloud.
Security Information and Event Management (SIEM): Splunk, QRadar, Microsoft Sentinel.
Data Loss Prevention (DLP): Forcepoint DLP, Symantec DLP.
Network Security Tools: Firewalls, Intrusion Prevention Systems (IPS).
Best Practices for Success:
Start with a Plan: Develop a comprehensive security strategy before implementing any changes.
Prioritize Security Training: Train your team on hybrid cloud security best practices and cloud-specific security threats.
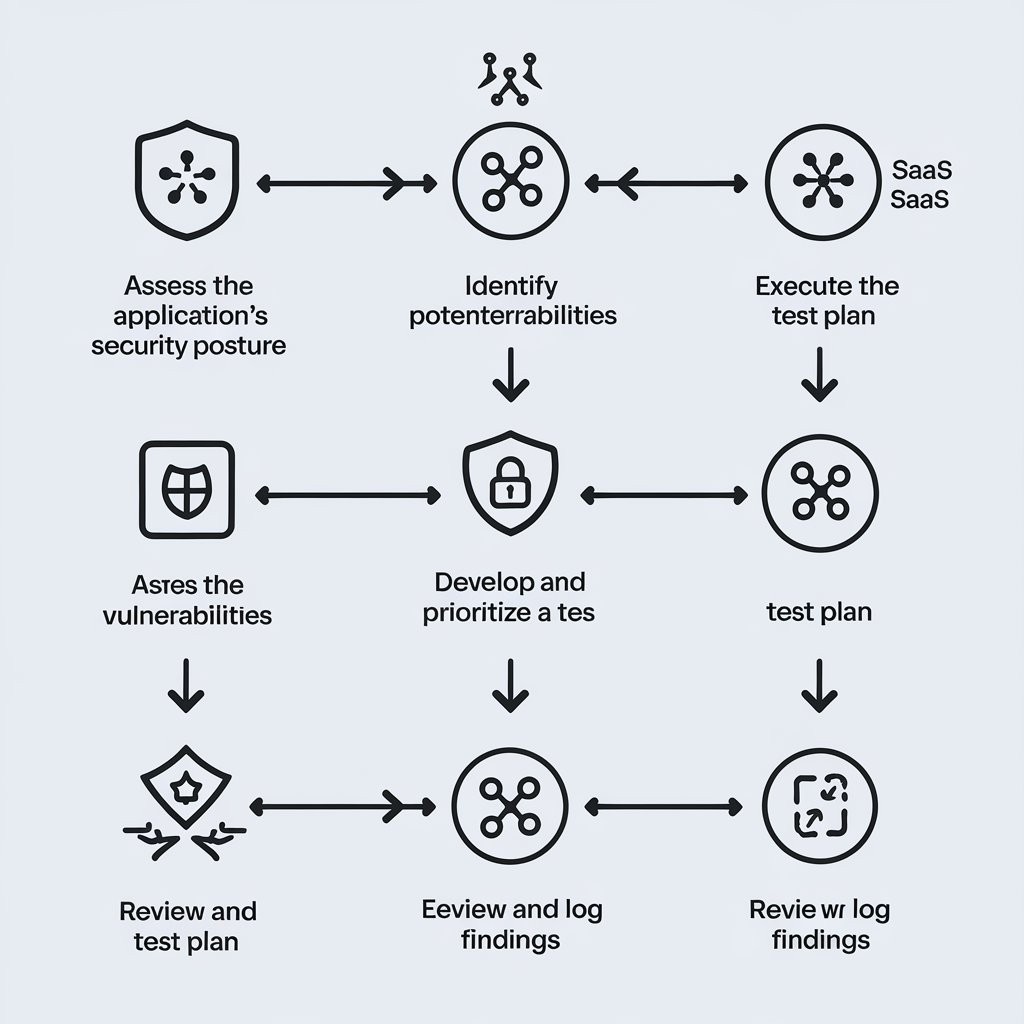
Regularly Audit and Test: Conduct regular audits and penetration tests to identify weaknesses and improve your security posture.
Stay Up-to-Date: Keep abreast of the latest cloud security best practices and threats.
Conclusion:
Managing security in hybrid cloud environments is challenging but not insurmountable. By implementing a unified security strategy, focusing on identity and access management, enhancing network security, prioritizing data protection, and improving visibility and monitoring, you can effectively secure your hybrid cloud environment and reap the benefits of this powerful model.
Call to Action:
What challenges are you facing in managing your hybrid cloud security?
What strategies have been successful for you?
Share your experiences and ask questions in the comments below!
Key takeaways from this blog post:
Clear Definition: Provides a solid definition of a hybrid cloud environment.
Addresses Challenges: Directly addresses the unique security challenges of hybrid clouds.
Actionable Strategies: Offers concrete strategies and best practices.
Tools and Technologies: Provides a useful list of relevant tools.
Best Practices: Includes actionable best practices for success.
Engaging Call to Action: Prompts readers to engage in a discussion. audit3aa
Join our newsletter list
Sign up to get the most recent blog articles in your email every week.